[ AI Augmentation Protocol ]
Target: Local Development
Status: Operational
Target: Local Development
Status: Operational
System Ready
Execute
Security.
Your AI just became a senior security engineer. One command. 29 battle-tested security checks built into every coding assistant you already use.
[ Installation Vector ]
❯npx @netxeo/security-skill
[ Technical Specs ]
Security Modules
0
CWE Covered
0
OWASP Lists
0×
ASVS Level
0
[ Installation Setup ]
Smart detection
npx @netxeo/security-skill
USER > npx @netxeo/security-skill
╔══════════════════════════════════════════════╗ ║ 🔐 SECURITY SKILL Interactive Setup ║ ╚══════════════════════════════════════════════╝ Language : TypeScript / Node.js Deployment : Vercel AI tools : cursor, windsurf, gemini Let's tailor security coverage to your project. (~60 seconds)
? What type of project is this? Web application / API
? What infrastructure does it run on? Serverless / edge
? What features does it include? User auth, Database
? Any compliance requirements? EU users / GDPR
? Additional security hardening? Supply chain security
📦 Installing tailored security-skill...
✅ Skill files installed → .skills/security/
✅ .gitignore updated (6 security entries added)
✅ .gitignore updated (6 security entries added)
Configuring AI assistants...
✅ .cursor/rules/security.mdc ← Cursor
✅ GEMINI.md created ← Gemini
✅ .windsurfrules created ← Windsurf
✅ GEMINI.md created ← Gemini
✅ .windsurfrules created ← Windsurf
_
[ Execution Log ]
What happens after
/security-audit
USER > /security-audit
🔍 Detecting stack... Next.js · Supabase · Vercel · Node 20
📋 Running 25 security checks across 29 modules...
====================================== 🔒 SECURITY AUDIT — myproject Stack: Next.js · Supabase · Vercel ====================================== SCORE : 61 / 100 [ WARNING ] ====================================== [!] Secrets & Files 12/20 ← FIX [+] Auth & Sessions 18/20 [!] Database (RLS) 8/20 ← FIX [-] HTTP Headers 13/20 [+] Source Code 18/20 ======================================
🔴CRITICAL — Supabase service role key exposed in frontend
Any visitor gets full DB access · Execute:
Any visitor gets full DB access · Execute:
/security-fix supabase-key🟡HIGH — RLS disabled on 3 tables (users, orders, messages)
Authenticated users can read all rows · Execute:
Authenticated users can read all rows · Execute:
/security-fix rls_
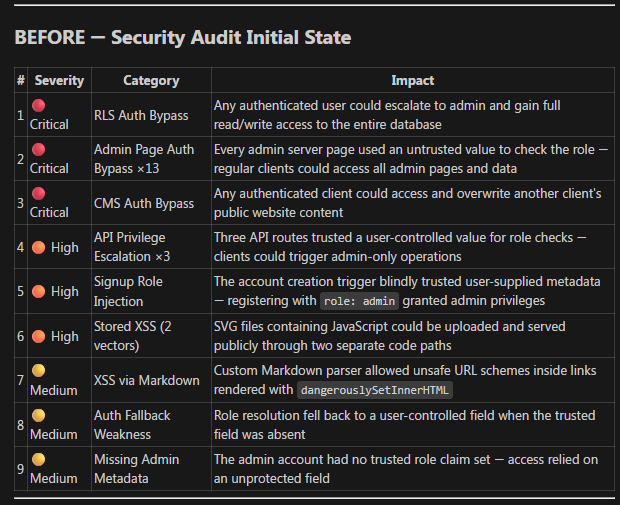
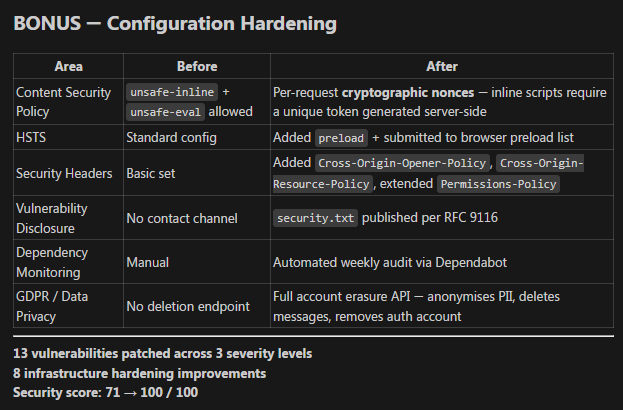
[ Visual Evidence ]
Without Protocol
With Protocol Active
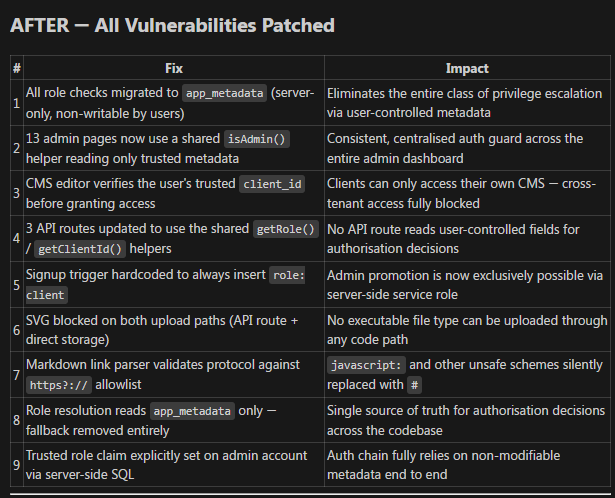
Execution Output
[ Implementation Protocol ]
[01]
Smart interactive setup.
npx @netxeo/security-skillA 1-minute prompt detects your exact stack (Web, Docker, AI) and installs targeted modules. Or use --yes to install all.
[02]
Your AI becomes the expert.
/security-scanAuto-detects your stack — Next.js, Firebase, Docker — and runs targeted checks. No guessing, no false positives.
[03]
Review & fix. Your call.
/security-fixSee the exact diff before anything changes. Every fix is explained. Non-breaking. Approved by you.
[ Feature Matrix ]
[01]
Scans in 30 seconds
No build step. No cloud. Pure AI pattern recognition on your actual codebase.
[02]
You approve every fix
The AI proposes a diff. You decide. Nothing changes without your explicit approval.
[03]
Security score /100
Tracked in memory-security.md. You'll watch your score climb with every fix.
[04]
Any stack, anywhere
Next.js, Express, Django, Laravel, Spring Boot. Auto-detected from your project.
[05]
Context-rich findings
Each vulnerability includes the attack vector, real-world impact, and a tailored fix.
[06]
Persistent memory
Accepted risks, rotation schedules — your AI remembers across every session.
[ Engine Compatibility ]
ClaudeCLAUDE.md
GitHub Copilotcopilot-instructions.md
Cursor.cursorrules
Windsurf.windsurfrules
Cline.clinerules
OpenAI CodexAGENTS.md
Continue.dev.continue/config.yaml
Aider.aider.conf.yml
GeminiGEMINI.md